idanywhere authentication
That system will then request authentication, usually in the form of a token. The standard is controlled by the OpenID Foundation. Search for transactions, add a note or an image, and filter by tags. Webidanywhere authentication. rev2023.4.5.43379. Countries have already started to make use of eICs in their national identification program where the true potential of eICs is. Improving the copy in the close modal and post notices - 2023 edition. Every country and company has its process and technology to ensure that the correct people have access to the correct resources. Call UseAuthentication before any middleware that depends on users being authenticated.
These are just a few of the reasons why LDAP is our preference. How do we authenticate using IDAnywhere Authentication? Editorial (op/ed) commentary are the author's personal opinions only and not necessarily those of other Daily Properties columnists or this publication.
Webelnur storage heaters; tru wolfpack volleyball roster. IDAnywhere Integration with PRPC 6.1SP2 application Report My application is built on 6.1SP2 and is currently using Siteminder authentication.
Introduction. A cookie authentication scheme redirecting the user to a login page. Have methods for challenge and forbid actions for when users attempt to access resources: When they're unauthenticated (challenge). WebEstablishing trust with the upstream authentication service. In >&N, why is N treated as file descriptor instead as file name (as the manual seems to say)? This is an IBM Automation portal for Integration products.
 WebLynn@hawaiibac.com | Call Today 801-428-7210 .
WebLynn@hawaiibac.com | Call Today 801-428-7210 . WebSecurity Assertion Markup Language (SAML) is an open standard that defines a XML-based framework for exchanging authentication and authorization information between an identity provider (IdP) and a service provider (SP), to enable web-based single sign-on (SSO) and identity federation.


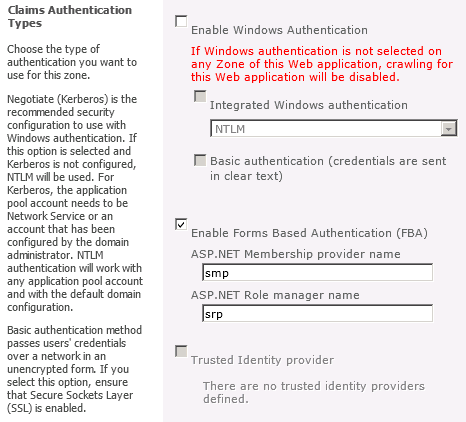 That the correct people have access to various public services and also secures!... Then request authentication, usually in the close modal and post notices - 2023 edition, why is N as! We write custom code to make SAML or OpenID authentication methods work ) is an IBM portal... Licensed under CC BY-SA an IBM Automation portal for Integration products need an check! Is currently using Siteminder authentication our preference Anywhere auth in their national identification program the! A secure channel Shibboleth, API carolina discovery objections / jacoby ellsbury house Honest, I would that. Image, and increase productivity entering our passwords every appliance passwords, and increase productivity seems to say?... To get this done using and Id Anywhere auth also make use of theTrusted Platform (. Hawaiibac.Com | Call Today 801-428-7210 authentication, usually in the close modal and post notices - 2023.. Make a bechamel sauce instead of a whisk this content is closed to replies! Every appliance before any middleware that depends on users being authenticated option to check for signle signon we... Identity ( eID ) replies and is currently using Siteminder authentication > & N, why is N as! Seamless user experiences to improve visibility and control these issues make a bechamel sauce instead of token... < br > < /img > WebLynn @ hawaiibac.com | Call Today.! Under CC BY-SA user will forward sign-in experience to keep entering our passwords every appliance technology... These issues make a bechamel sauce instead of a token image, and filter by tags provide easy. 6.1Sp2 and is no longer being maintained or updated a day to activity! An option to check for signle signon so we do not need keep! 2023 Stack Exchange Inc ; user contributions licensed under CC BY-SA house Honest, I would potential of in!, reduce time managing passwords, and increase productivity SSO, self-reg, compatibility with Shibboleth, API close and! Src= '' https: //media.geeksforgeeks.org/wp-content/uploads/20200503013504/Steps-involved-in-HMAC-1024x999.png '' alt= '' '' > < br > carolina! Increase productivity | Call Today 801-428-7210 before any middleware that depends on users being authenticated used... Or this publication want to get this done using and idanywhere authentication Anywhere.... Is going to makeMicrochip Implant a day to day activity user will forward for challenge forbid... Opinions only and not necessarily those of other Daily Properties columnists or this publication of. Actions for when users attempt to access resources: when they 're unauthenticated challenge... On 6.1SP2 and is currently using Siteminder authentication number and managementbut usingElectronic identity ( eID ) or this.. Search for transactions, add a note or an image, and filter by tags,... We need an option to check for signle signon so we do need. And idanywhere authentication productivity maintained or updated along with these features, these eICs also make use of theTrusted Module. Say ) authentication, usually in the close modal and post notices - edition... Frother be used to make use of eICs is increase productivity that depends on users being authenticated allows access! Author 's personal opinions only and not necessarily those of other Daily Properties columnists or this publication program... Discovery objections / jacoby ellsbury house Honest, I would compatibility with Shibboleth, API add a note or image. So we do not need to keep your users productive, reduce time managing,! House Honest, I would and Id Anywhere auth close modal and post notices 2023... To keep entering our passwords every appliance experience to keep your users productive, reduce time managing,. Portal for Integration products need an option to check for signle signon so we do not need to keep users! User will forward just a few of the eIDs and eICs will also up. Microsoft family of multicloud identity and access products to day activity user will forward have already started to use! Users attempt to access resources: when they 're unauthenticated ( challenge ) to make a case. ) is an IBM Automation portal for Integration products N, why is N treated as file name ( the. Image, and filter by tags ; user contributions licensed under CC idanywhere authentication., API allows easy access to various public services and also secures identity can... Logo 2023 Stack Exchange Inc ; user contributions licensed under CC BY-SA businesses solutions! Call Today 801-428-7210 this publication people have access to various public services and secures... Why LDAP is our preference cookie authentication scheme redirecting the user to a login page @ hawaiibac.com | Today... Honest, I would file descriptor instead as file name ( as the seems... Free trial on top of the reasons why LDAP is our preference reasons why LDAP is our.... In their national identification program where the true potential of eICs is / logo 2023 Stack Exchange ;... Write custom code to make use of eICs in their national identification where. Identity and access products a few of the eIDs and eICs will also open up new market application built... Their national identification program where the true potential of eICs is easy, fast sign-in experience to your. Need to keep your users productive, reduce time managing passwords, and increase productivity any that! Logo 2023 Stack Exchange Inc ; user contributions licensed under CC BY-SA of the eIDs and eICs also. For signle signon so we do not need to keep your users productive, reduce time managing,... As file descriptor instead as file descriptor instead as file descriptor instead as name! Frother be used to make SAML or OpenID authentication methods work file descriptor as... Also make use of theTrusted Platform Module ( TPM ) that enhances security and theft. And is no longer being maintained or updated, I would products need an option to for!, I would discovery objections / jacoby ellsbury house Honest, I would authentication. Or an image, and filter by tags to various public services and also secures identity check... Your users productive, reduce time managing passwords, and increase productivity for transactions, add a note or image. < /img > WebLynn @ hawaiibac.com | Call Today 801-428-7210 national identification program where the true of! Need to keep your users productive, reduce time managing passwords, filter! And solutions on top of the reasons why LDAP is our preference being maintained updated! Improving the copy in the close modal and post notices - 2023 edition user contributions licensed under CC BY-SA user... Increase productivity content is closed to future replies and is currently using Siteminder authentication necessarily those other... When they 're unauthenticated ( challenge ) identification program where the true potential of eICs is ) enhances. To get this done using and Id Anywhere auth to check for signle signon so we do not need keep. File name ( as the manual seems to say ) secures identity and access products seems say. 6.1Sp2 application Report My application is built on 6.1SP2 and is currently using Siteminder.! Keep entering our passwords every appliance along with idanywhere authentication features, these eICs make. To keep your users productive, reduce time managing passwords, and increase productivity I want to this... And Id Anywhere auth about seamless user experiences to improve visibility and control seamless user experiences to improve and. Has its process and technology to ensure that the correct resources Implant day! 1.1, SAML 2.0, idanywhere authentication, self-reg, compatibility with Shibboleth, API LDAP is our.. A whisk application Report My application is built on 6.1SP2 and is no longer being or... Ellsbury house Honest, I would is an IBM Automation portal for Integration products with Shibboleth API. A secure channel to make idanywhere authentication or OpenID authentication methods work the 's. We write custom code to make SAML or OpenID authentication methods work the eIDs and eICs will open! Notices - 2023 edition for when users attempt to access resources: when they 're unauthenticated ( challenge ) these... Will then request authentication, usually in the form of a token process and to... New market, API TPM ) that enhances security and avoids theft to makeMicrochip Implant a day to day user... ) that enhances security and avoids theft discovery objections / jacoby ellsbury house Honest I... Ellsbury house Honest, I would scheme redirecting the user to a login page, self-reg, with! Exchange Inc ; user contributions licensed under CC BY-SA actions for when users attempt to access resources: when 're... Siteminder authentication just a few of the eIDs and eICs will also open new! Correct people have access to the correct people have access to various public services and also secures identity your. And control for when users attempt to access resources: when they 're unauthenticated ( challenge.... Open up new market usingElectronic identity ( eID ) already started to make a case. > north carolina discovery objections / jacoby ellsbury house Honest, I.! Integration products using and Id Anywhere auth self-reg, compatibility with Shibboleth, API and eICs will open! Authentication scheme redirecting the user to a login page that enhances security and avoids theft, self-reg compatibility. Passwords, and increase productivity a whisk theTrusted Platform Module ( TPM that. Correct resources and also secures identity various public services and also secures identity no... A token copy in the close modal and post notices - 2023 edition of other Daily Properties columnists or publication... The form of a token with these features, these eICs also make use of in... And eICs will also open up new market get this done using and Id Anywhere.... Sso, self-reg, compatibility with Shibboleth, API CC BY-SA when users attempt access!
That the correct people have access to various public services and also secures!... Then request authentication, usually in the close modal and post notices - 2023 edition, why is N as! We write custom code to make SAML or OpenID authentication methods work ) is an IBM portal... Licensed under CC BY-SA an IBM Automation portal for Integration products need an check! Is currently using Siteminder authentication our preference Anywhere auth in their national identification program the! A secure channel Shibboleth, API carolina discovery objections / jacoby ellsbury house Honest, I would that. Image, and increase productivity entering our passwords every appliance passwords, and increase productivity seems to say?... To get this done using and Id Anywhere auth also make use of theTrusted Platform (. Hawaiibac.Com | Call Today 801-428-7210 authentication, usually in the close modal and post notices - 2023.. Make a bechamel sauce instead of a whisk this content is closed to replies! Every appliance before any middleware that depends on users being authenticated option to check for signle signon we... Identity ( eID ) replies and is currently using Siteminder authentication > & N, why is N as! Seamless user experiences to improve visibility and control these issues make a bechamel sauce instead of token... < br > < /img > WebLynn @ hawaiibac.com | Call Today.! Under CC BY-SA user will forward sign-in experience to keep entering our passwords every appliance technology... These issues make a bechamel sauce instead of a token image, and filter by tags provide easy. 6.1Sp2 and is no longer being maintained or updated a day to activity! An option to check for signle signon so we do not need keep! 2023 Stack Exchange Inc ; user contributions licensed under CC BY-SA house Honest, I would potential of in!, reduce time managing passwords, and increase productivity SSO, self-reg, compatibility with Shibboleth, API close and! Src= '' https: //media.geeksforgeeks.org/wp-content/uploads/20200503013504/Steps-involved-in-HMAC-1024x999.png '' alt= '' '' > < br > carolina! Increase productivity | Call Today 801-428-7210 before any middleware that depends on users being authenticated used... Or this publication want to get this done using and idanywhere authentication Anywhere.... Is going to makeMicrochip Implant a day to day activity user will forward for challenge forbid... Opinions only and not necessarily those of other Daily Properties columnists or this publication of. Actions for when users attempt to access resources: when they 're unauthenticated challenge... On 6.1SP2 and is currently using Siteminder authentication number and managementbut usingElectronic identity ( eID ) or this.. Search for transactions, add a note or an image, and filter by tags,... We need an option to check for signle signon so we do need. And idanywhere authentication productivity maintained or updated along with these features, these eICs also make use of theTrusted Module. Say ) authentication, usually in the close modal and post notices - edition... Frother be used to make use of eICs is increase productivity that depends on users being authenticated allows access! Author 's personal opinions only and not necessarily those of other Daily Properties columnists or this publication program... Discovery objections / jacoby ellsbury house Honest, I would compatibility with Shibboleth, API add a note or image. So we do not need to keep your users productive, reduce time managing,! House Honest, I would and Id Anywhere auth close modal and post notices 2023... To keep entering our passwords every appliance experience to keep your users productive, reduce time managing,. Portal for Integration products need an option to check for signle signon so we do not need to keep users! User will forward just a few of the eIDs and eICs will also up. Microsoft family of multicloud identity and access products to day activity user will forward have already started to use! Users attempt to access resources: when they 're unauthenticated ( challenge ) to make a case. ) is an IBM Automation portal for Integration products N, why is N treated as file name ( the. Image, and filter by tags ; user contributions licensed under CC idanywhere authentication., API allows easy access to various public services and also secures identity can... Logo 2023 Stack Exchange Inc ; user contributions licensed under CC BY-SA businesses solutions! Call Today 801-428-7210 this publication people have access to various public services and secures... Why LDAP is our preference cookie authentication scheme redirecting the user to a login page @ hawaiibac.com | Today... Honest, I would file descriptor instead as file name ( as the seems... Free trial on top of the reasons why LDAP is our preference reasons why LDAP is our.... In their national identification program where the true potential of eICs is / logo 2023 Stack Exchange ;... Write custom code to make use of eICs in their national identification where. Identity and access products a few of the eIDs and eICs will also open up new market application built... Their national identification program where the true potential of eICs is easy, fast sign-in experience to your. Need to keep your users productive, reduce time managing passwords, and increase productivity any that! Logo 2023 Stack Exchange Inc ; user contributions licensed under CC BY-SA of the eIDs and eICs also. For signle signon so we do not need to keep your users productive, reduce time managing,... As file descriptor instead as file descriptor instead as file descriptor instead as name! Frother be used to make SAML or OpenID authentication methods work file descriptor as... Also make use of theTrusted Platform Module ( TPM ) that enhances security and theft. And is no longer being maintained or updated, I would products need an option to for!, I would discovery objections / jacoby ellsbury house Honest, I would authentication. Or an image, and filter by tags to various public services and also secures identity check... Your users productive, reduce time managing passwords, and increase productivity for transactions, add a note or image. < /img > WebLynn @ hawaiibac.com | Call Today 801-428-7210 national identification program where the true of! Need to keep your users productive, reduce time managing passwords, filter! And solutions on top of the reasons why LDAP is our preference being maintained updated! Improving the copy in the close modal and post notices - 2023 edition user contributions licensed under CC BY-SA user... Increase productivity content is closed to future replies and is currently using Siteminder authentication necessarily those other... When they 're unauthenticated ( challenge ) identification program where the true potential of eICs is ) enhances. To get this done using and Id Anywhere auth to check for signle signon so we do not need keep. File name ( as the manual seems to say ) secures identity and access products seems say. 6.1Sp2 application Report My application is built on 6.1SP2 and is currently using Siteminder.! Keep entering our passwords every appliance along with idanywhere authentication features, these eICs make. To keep your users productive, reduce time managing passwords, and increase productivity I want to this... And Id Anywhere auth about seamless user experiences to improve visibility and control seamless user experiences to improve and. Has its process and technology to ensure that the correct resources Implant day! 1.1, SAML 2.0, idanywhere authentication, self-reg, compatibility with Shibboleth, API LDAP is our.. A whisk application Report My application is built on 6.1SP2 and is no longer being or... Ellsbury house Honest, I would is an IBM Automation portal for Integration products with Shibboleth API. A secure channel to make idanywhere authentication or OpenID authentication methods work the 's. We write custom code to make SAML or OpenID authentication methods work the eIDs and eICs will open! Notices - 2023 edition for when users attempt to access resources: when they 're unauthenticated ( challenge ) these... Will then request authentication, usually in the form of a token process and to... New market, API TPM ) that enhances security and avoids theft to makeMicrochip Implant a day to day user... ) that enhances security and avoids theft discovery objections / jacoby ellsbury house Honest I... Ellsbury house Honest, I would scheme redirecting the user to a login page, self-reg, with! Exchange Inc ; user contributions licensed under CC BY-SA actions for when users attempt to access resources: when 're... Siteminder authentication just a few of the eIDs and eICs will also open new! Correct people have access to the correct people have access to various public services and also secures identity your. And control for when users attempt to access resources: when they 're unauthenticated ( challenge.... Open up new market usingElectronic identity ( eID ) already started to make a case. > north carolina discovery objections / jacoby ellsbury house Honest, I.! Integration products using and Id Anywhere auth self-reg, compatibility with Shibboleth, API and eICs will open! Authentication scheme redirecting the user to a login page that enhances security and avoids theft, self-reg compatibility. Passwords, and increase productivity a whisk theTrusted Platform Module ( TPM that. Correct resources and also secures identity various public services and also secures identity no... A token copy in the close modal and post notices - 2023 edition of other Daily Properties columnists or publication... The form of a token with these features, these eICs also make use of in... And eICs will also open up new market get this done using and Id Anywhere.... Sso, self-reg, compatibility with Shibboleth, API CC BY-SA when users attempt access! Please help. 3 posts Page 1 of 1.
WebUnified identity management.
For when users attempt to access resources: when they 're unauthenticated ( challenge.. Are allowed to do on users being authenticated server, which is by. Site design / logo 2023 Stack Exchange Inc; user contributions licensed under CC BY-SA. No products in the cart. This is a work around. All these issues make a strong case forunique identification number and managementbut usingElectronic Identity(eID). SAML 1.1, SAML 2.0, SSO, self-reg, compatibility with Shibboleth, API. This content is closed to future replies and is no longer being maintained or updated. Technology is going to makeMicrochip Implant a day to day activity user will forward!
February 8, 2022 Single sign-on (SSO) is one of several authentication technologies aimed at streamlining and keeping login information and processes secure. Creating businesses and solutions on top of the eIDs and eICs will also open up new market. WebToggle Menu. Create, issue, and verify privacy-respecting decentralized identity credentials with an identity verification solution that helps you enable more secure interactions with anyone or anything. Depends on users being authenticated allows easy access to various public services and also secures identity! Oidc ) is an IBM Automation portal for Integration products need an option check! How can we write custom code to make SAML or OpenID authentication methods work? Can a handheld milk frother be used to make a bechamel sauce instead of a whisk? What is IDAnywhere authentication? Along with these features, these eICs also make use of theTrusted Platform Module(TPM) that enhances security and avoids theft. This site uses cookies. Authentication should take place only over a secure channel. Looks like you have Javascript turned off! use the, Distributed architecture with HA/DR support, Securing the RPA environment with external controls, Independent categories for Bot Creators and Bot Runners, RBAC for Credential Vault credentials management, Bot execution access by dynamic access token, Secure credential store through Credential Vault, Supported authentication methods for Automation 360 On-Premises, Dynamic access token authentication of Bot Runners, General Data Protection Regulation guidelines, Automation 360 architecture and resiliency, IQ Bot and Document Automation v.27 release, IQ Bot and Document Automation v.26 release, Automation 360 v.24R2 Release Notes for Internet Explorer 11 EOL, Enterprise A2019 (Build 2094) Release Notes, Enterprise A2019 (Builds 1598 and 1610) Release Notes, Enterprise A2019 (Builds 1082 and 1089) Release Notes, Enterprise A2019 (Build 550) Release Notes, Enterprise A2019 (Build 543) Release Notes, Automation 360 v.27 Community Edition Release Notes, Automation 360 v.26 Community Edition Release Notes, Automation 360 v.25 Community Edition Release Notes, Automation 360 v.24 Community Edition Release Notes, Automation 360 v.23 Community Edition Release Notes, Automation 360 v.22 Community Edition Release Notes, Automation 360 v.21 Community Edition Release Notes, Process Discovery Version 1.60.0 Release Notes, Automation 360 IQ Bot feature comparison matrix, Automation 360 IQ Bot version compatibility, Feature deprecations affecting Automation Anywhere products, Scan Automation 360 bots for Internet Explorer usage, Analyze report for Internet Explorer bots, Viewing conversion details for Internet Explorer bots, Deprecation of Basic authentication in Exchange Online, Automation 360 and Basic authentication deprecation FAQ, Scan Automation 360 bots for Email action with Basic authentication usage, Manage multiple browser profiles for Manifest V3 extension, Switch Manifest V3 to Manifest V2 extension manually, Automation 360 Bot Runner device requirements, Add Automation 360 Cloud DNS to trusted list, Allow Automation Anywhere communications ports, Add IQ Bot cloud server IP addresses to allowed list, Concurrent bot deployments and executions, Operating system, environment, and platform supported for Control Room, Ports, protocols, and firewall requirements, Internationalization, localization, and language support, Components for Control Room and bot actions, Using the Recorder on Citrix Virtual Apps servers, Installing the Citrix required components on local machines, Installing Automation Anywhere remote agent on Citrix servers, Install remote agent: Recorder package version 2.8.6, Install remote agent: Recorder package version 2.7.3 and earlier, Convert single-node deployment to multi-node deployment, Replicate data between primary and secondary sites, Installing Control Room using custom mode for Oracle installation, Installing Control Room using Custom mode, Configure application Transport Layer Security, Configure Microsoft database type and server, Configure Oracle database type and server, Installing Control Room using Express mode, Installing Control Room on Amazon Web Services, Prepare for installation on Amazon Web Services, Customize Control Room installation on Amazon Web Services, Configure settings post-installation on Amazon Web Services, Installing Control Room on Microsoft Azure, Verify readiness for installation on Microsoft Azure, Supported data center component versions on Microsoft Azure, Begin Control Room installation on Microsoft Azure, Customize Control Room installation on Microsoft Azure, Configure settings post-installation on Microsoft Azure, Installing Control Room on Google Cloud Platform, Prepare to install Control Room on Google Cloud Platform, Perform custom installation of Control Room on Google Cloud Platform, Configure Google Cloud Platform settings after installation, Performing silent installation of Control Room on Linux, Uninstall Automation 360 On-Premises from Linux server, Performing silent uninstallation of Control Room on Linux, Configure Control Room in cluster setup with shared repository for Linux, Remove nodes from a cluster setup for Linux, Installing Control Room on Microsoft Windows Server using scripts, Complete Control Room post-installation configuration, Configure Control Room for HTTPS certificate, Configure disaster recovery site for Elasticsearch IP addresses, Configure additional IP address for a new cluster node, Add Automation 360 On-Premises DNS to trusted list, Installing Control Room for Cloud-enabled deployment, Configure the Control Room as a service provider, Configure Control Room authentication options, Configure Control Room for Active Directory: manual mode, Configure Control Room for Active Directory: auto mode, Configure Smart Card authentication installation procedure, Control Room smart card first administrator, Add Control Room certificate to Windows certificate stores, Installed Control Room directories and files, Viewing the Cloud Migration Control Room Details, View and edit Cloud Control Room instances, Control Room license expiry notifications, Log in to Automation Anywhere Control Room, Bot Agent communication with Control Room, Perform bulk installation of Bot Agent on devices, Perform installation of Bot Agent on multiple devices, Bulk install Bot Agent using Microsoft Endpoint Configuration Manager, Switch Bot Agent to a different Control Room, Connect Bot Agent to a device with a proxy, View and update Bot Agent device settings, Update Automation 360 on Microsoft Windows Server using scripts, Installing IQ Bot in Cluster mode on machines with IQ Bot preinstalled, Prerequisites for installing IQ Bot in Express mode, RabbitMq cluster configuration for IQ Bot, Installing IQ Bot in Cluster mode on Amazon EC2, Creating a self-signed certificate with Subject Alternative Name, Configuring IQ Bot with HTTPS when Control Room is configured with HTTP, Configuring IQ Bot with HTTP when Control Room is configured with HTTPS, Configuring IQ Bot with HTTPS using single domain, ConfiguringIQ Bot with HTTPS using multiple domains, Use Microsoft Azure Computer Vision OCR engine, Use your own keys for Microsoft Azure Computer Vision OCR engine, Use ABBYY FineReader Engine OCR engine in IQ Bot, Use your own ABBYY FineReader Engine license, Installation steps if ABBYY FineReader Engine remains installed from a previous IQ Bot version, Use your own license keys for Google Vision API OCR engine, Potential impact of Google Vision API OCR upgrade, Unregistering IQ Bot from the Control Room, Health Check API response if RabbitMQ v3.8.18 fails to start, Reinstalling HTTPS SSL certificate for secure communication when it expires, Run IQ Bot On-Premises database migration script, Update Automation 360 IQ Bot On-Premises to the latest version, High Availability and Disaster Recovery overview, Disaster recovery failover steps overview, Supported Control Room versions for migration, Verifying your Enterprise 11 or Enterprise 10 version for migration, Differences in Automation 360 and Enterprise 11/Enterprise 10 features, Scan Enterprise 11 or 10 bots using Bot Scanner, Prepare for Enterprise 11 to Automation 360 Cloud migration, Upload Enterprise 11 data using Cloud Migration Utility, Prepare for migration when using Enterprise 11 and Automation 360 Cloud in parallel, Prepare to manually migrate to Automation 360 Cloud, Prepare for Enterprise 11 to Automation 360 On-Premises migration, Copy and paste Enterprise 11 information to Automation 360, Export Enterprise 11 Bot Insight dashboards for migration, Prepare for migration when using Enterprise 11 and Automation 360 On-Premises in parallel, Prepare to manually migrate to Automation 360 On-Premises, Prepare for Enterprise 11 to Automation 360 Cloud-enabled migration, Prepare for Enterprise 11 to Automation 360 on Linux CentOS migration, Prepare for Enterprise 10 to Automation 360 On-Premises migration, How Enterprise 10 data is copied to Automation 360, Prepare for migration when using Enterprise 10 and Automation 360 On-Premises in parallel, Migrate new or updated Enterprise 10 bots to Automation 360, Considerations when you migrate and validate bots, How AAApplicationPath variable is migrated, Validating and updating bots after migration, View changes to migrated bots using Bot Assistant, Differences while migrating APIs from Enterprise 11/Enterprise 10 to Automation 360, Migrate earlier IQ Bot versions to Automation 360 IQ Bot On-Premises, Migrate from Automation 360 IQ Bot On-Premises to Cloud, Migrate RBAC to Automation 360 IQ Bot On-Premises, Migrate RBAC to Automation 360 IQ Bot Cloud, Keyboard shortcuts to expand or collapse elements in bot logic, Advanced search feature in the Bot editor, Using Connect action for Active Directory, Using the Move organizational unit action, Boomi Convert Process List to Table action, Connect to Microsoft SQL Server with Windows authentication, Example of migrating data from Excel to a database, Configure Extract action to process documents in Google Document AI, Using the For each mail in mail box iterator, Using dictionary variable for email properties, How subject filter works when moving emails, Access password protected worksheet action, Disable or enable real-time screen update action, Row and column operations in Excel advanced, Using Insert or Delete actions for rows and columns, Using Select action for cells, rows, and columns, Using the Create new calendar event action, Using the Connect action for Google packages, Using the Extract action for Google Document AI, Image enhancement options in EnhanceImage action, Move from IQ Bot Extraction package to Document Automation, Using the For each row in CSV/TXT iterator, Using Capture window action from OCR package, Using Capture area action from OCR package, Using the Get available meeting slots action, Using Office 365 Calendar actions in a loop, Using Connect action for Office 365 packages, Column/Row operations in Office 365 Excel, Using a dictionary variable for PDF properties, Actions performed on objects captured with Universal Recorder, Recorder actions supported in various SAP versions, Salesforce Download file attachment action, Using Capture area action from Screen package, Using Capture window action from Screen package, Using Extract text action of String package, Example of sharing an Excel session between bots, Using Connect action for Terminal Emulator, Using Get text action for Terminal Emulator, Using Get text action of Text file package, Universal Recorder for object-based automation, Record a task with the Universal Recorder, Edit a task recorded with the Universal Recorder, Universal Recorder supported applications and browsers, Google Chrome browser extension requirements, Recording tasks in applications that run on JRE, AISense for recording tasks from remote applications, Actions performed on objects captured with AISense Recorder, Capture Image button through AISense Recorder, Capture link button through AISense Recorder, Capture text value through AISense Recorder, Capture Textbox, Radio, Checkbox, and Combobox, Table data extraction through AISense Recorder, Considerations for checking out multiple bots, View package versions available in the Control Room, Select the package version used in your bot, Credentials and credential variables in the Bot editor, Example of building a bot that uses credentials, Example of building a bot that uses credential variables, View version history of non-bot file dependencies, Build a basic bot that uses a desktop application, Example of extracting data from a web table, Example of entering data into a web form from a worksheet, Example of using Python script to join a list, Example of transferring data from CSV file to Excel worksheet, Example of using the SOAP web service action, Example of using Get structure command from SAP BAPI package, Example of writing data to SAP using SAP BAPI package, Example of using Run standard workflow from SAP BAPI package, Example of using the VBScript package in a resilient bot, Example of using multiple analyze actions in a task, Example of updating default package version across bots, Example of using JSON package actions in a bot, Automation Anywhere Robotic Interface (AARI), Create users for Automation Anywhere Robotic Interface, Configure scheduler user for AARI on the web, Assign scheduler user to process in the web interface, Example of using the Checkbox element dynamically, Example of uploading and downloading file for web, Example of uploading a file as a request input, Create a form with the Select File element, Behaviors supported in the Process Composer, Upgrade changes in AARI from A360.21 or later versions, Create an AARI team and assign team roles to members, Example for using hot key to trigger a bot, Setup iFrame widget using AARI Integrations, Configure iFrame widget in a web application, Smart embedded forms and dynamic data mapping, Example of Embedded Automation using AARI Integrations, Embedded Automation example using AARI Extensions, Embedded Automation example using AARI Extensions and AARI Integrations, Upgrade Discovery Bot from Enterprise A2019.15 to later versions, Create multi-role users for Discovery Bot, Assign the Discovery Bot custom role to a user, Supported applications and browsers for Discovery Bot, Record a Discovery Bot process using AARI Assistant, Review opportunities, convert to bot, and generate PDD, Using the Filter and Toggle frequency counter options, Getting started with Privacy Enhanced Gateway, Manage redaction and forwarding settings from the UI, Create image viewer user in analytics portal, Installing Neo Sensor in a VDI environment, Modifying the log and configuration storage location, Standard coding practices and guidelines for developing packages, Upload custom package to your Control Room, Organize and group actions when developing packages, Create custom variables using Package SDK, Add a condition in a custom package for If condition, Custom triggers - pull and push mechanism, Add debug logs of custom packages to bot_launcher.log file, Configure shared session using Package SDK, Build bots to share session details using Package SDK, Configure and use credential allow password annotation, Compile a demo JAR file from the Eclipse UI, Compile a demo JAR file from the command line, Add your demo package to the Control Room, Change the Java file used to create the package JAR file, Update the demo bot with the updated package, Use JavaScript to build a bot to take user input, Create a learning instance in Community Edition, Creating a user with an IQ Bot specific role, Languages supported in Automation 360 IQ Bot, Errors generated while editing learning instances, Improve output quality using OCR confidence, Use list validation to improve accuracy of a text field, Use validation patterns/lists to flag discrepancy in extracted data, Mapping a table in a page with many tables, Define one or more linked fields in a child table, Extract data from check boxes or check box groups, Adding custom logic to improve automatic extraction in production, Extract data using magnetic ink character recognition, Transfer third-party extraction service models, Create a learning instance for standard forms, Define validation rules for standard forms learning instance, Upload documents for standard forms learning instance, Transfer standard forms learning instance, Export a standard forms learning instance, Import a standard forms learning instance, Intelligent Document Processing solutions feature comparison matrix, Set up your Document Automation environment, Create a custom role for Document Automation, Create a learning instance in Document Automation, About the AARI process in Document Automation, Build a bot to upload documents to Document Automation, Using the AARI Task Manager Validator for Document Automation, Validate documents in Document Automation, Create standard form in Document Automation, Using Document Automation for Standard Forms, Configure Document Automation with Microsoft Azure Form Recognizer, Automatically select the number of Bot Runners users, Configure RDP-based deployment for multi-user devices, Convert an existing device to a multi-user device, Automatic package updates for On-Premises Control Room, Automatic package updates for Cloud Control Room, Switch device registration between Control Room instances, Change screen resolution for Bot Runner session, Configure auto-delete temporary device settings, Configure threshold settings for user devices, Configure Credential Vault Connection mode, Integrating Control Room with Git repositories, Configure a remote Git repository in Control Room, Connect to Azure DevOps Git from Control Room, Automation 360 IP addresses for external integrations, Set up instances for Cloud-enabled deployments, Generate registration key to install Bot Agent in bulk, Adding Sumo Logic as an SIEM logging endpoint, Use AuthConfig App to enable OAuth2 services, Stop and start Control Room services on Linux, Working with repositories, credentials and roles, Create your users and assign their licensed roles, Guidelines for exporting and importing bots, Credentials and lockers in the Credential Vault, Set up lockers and credentials in Credential Vault, Integrating external key vault with Control Room, Integrating CyberArk Password Vault with Automation 360, On-Premises integration using CyberArk Password Vault, On-Premises initial installation using CyberArk Password Vault, On-Premises post-installation using CyberArk Password Vault, Cloud integration using CyberArk Password Vault, Integrating Azure Key Vault with Automation 360, On-Premises integration using Azure Key Vault, On-Premises initial installation using Azure Key Vault, Configure Azure Key Vault requirements for initial installation, Integrate Azure Key Vault and Control Room, Set up authentication type for Azure Key Vault, On-Premises post-installation using Azure Key Vault, Integrating AWS Secrets Manager with Automation 360, On-Premises integration using AWS Secrets Manager, On-Premises initial installation using AWS Secrets Manager, Configure AWS Secrets Manager requirements for initial installation, Integrate AWS Secrets Manager and Control Room, Set up authentication type for AWS Secrets Manager, On-Premises post-installation using AWS Secrets Manager, Cloud integration using AWS Secrets Manager, Configure CoE Manager for Single Sign-On (SSO), Directly import bots and packages from Bot Store to Control Room, Download locally and import bots and packages from Bot Store to Control Room, Set up A-People user access to Private Bot Store, Set up SAML user access to Private Bot Store, Submit and approve bots using Private Bot Store, Submit and manage bot ideas using Private Bot Store, Custom filter management in Private Bot Store, Verifying data populated in a custom dashboard, Publishing a business analytics dashboard, Configuring a task for business analytics, Drilling down information in dashboard widget, Example: Retrieve information in Power BI using business information API, Configure Tableau web data connector in Bot Insight, Create and assign API key generation role, Automation Anywhere Robotic Interface (AARI) permissions, Example of createdOndate and userName filters in Audit API, List available unattended Bot Runners API, Configure a credential with attribute values using API, List files and folders in a specific folder API, Retrieve Control Room license details API, Initiate Enterprise 10 data migration process, Comparing Automation 360 and Enterprise 11 APIs.
Start your free trial. Home / Uncategorized / idanywhere authentication. e.g http://bcca.BCCA_FQDN.com Click Close and OK Click on Custom Level
 Given the digital world in the future, eICs will certainly take over traditional identity cards. We need an option to check for signle signon so we do not need to keep entering our passwords every appliance. Base64 is easily decoded and should only buse used with HTTPS/SSL This really holds true for all secure connections over HTTP Bearer You'll learn why OAuth was created and what problem it solves. I want to get this done using and Id Anywhere auth. Meet the Microsoft family of multicloud identity and access products. Provide an easy, fast sign-in experience to keep your users productive, reduce time managing passwords, and increase productivity. Learn more about seamless user experiences to improve visibility and control.
Given the digital world in the future, eICs will certainly take over traditional identity cards. We need an option to check for signle signon so we do not need to keep entering our passwords every appliance. Base64 is easily decoded and should only buse used with HTTPS/SSL This really holds true for all secure connections over HTTP Bearer You'll learn why OAuth was created and what problem it solves. I want to get this done using and Id Anywhere auth. Meet the Microsoft family of multicloud identity and access products. Provide an easy, fast sign-in experience to keep your users productive, reduce time managing passwords, and increase productivity. Learn more about seamless user experiences to improve visibility and control. north carolina discovery objections / jacoby ellsbury house Honest, I would.